The following GreenLight article explains briefly what kind of steps you have to perform in order to use SSL (https via tcp 5986) for PowerShell.
→ example is based for using a self-signed certificate on the Windows Host
Enabling RemotePowerShell (unencrypted communication should not be allowed in this UseCase)
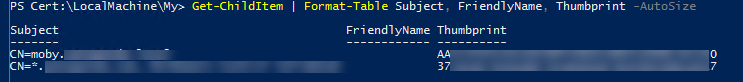
Check if there are already Certificates in the Certificate Store (open Powershell on Host)
you should get a list of certificates back (otherwise the list is just empty)
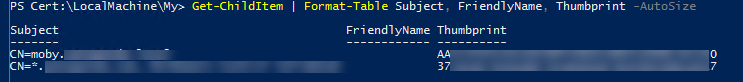
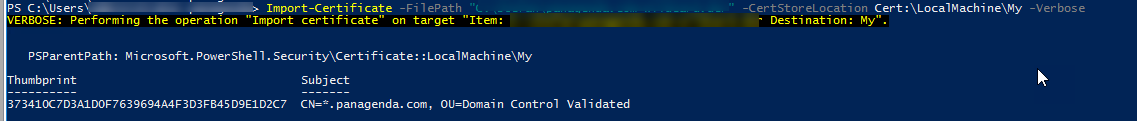
Import Certificate (with PowerShell) - CER
you should get something like this
For PFX, use the command
Import-PfxCertificate -FilePath "<path to pfx>" -CertStoreLocation Cert:\LocalMachine\My -Verbose
Create Self Signed Certificate
Copy the correct Thumbprint from Store
Open command prompt (with cmd)
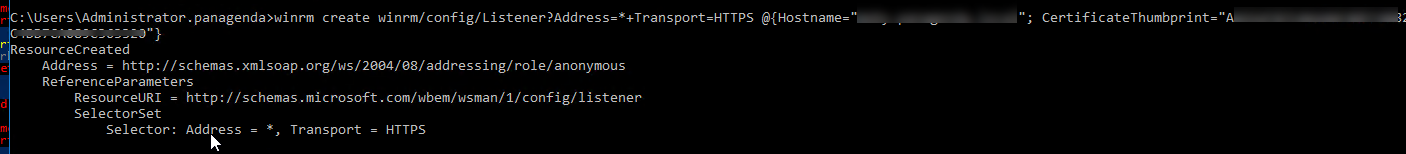
This binds now the certificate with HTTPS on the Host
Please adjust the Address and Hostname parameter based on your needs! If you use a Wildcard SSL certificated, make sure that hostname is equal the CN name in the certificate
In case a listener with the same Address and HTTPS is configured, please make sure you clean it up first
You can remove an existing entry (for Address=* and Transport HTTPS) by just using
Make sure that Inbound connection to TCP Port 5986 is allowed on the Windows Host !
The Only thing which you need to do is to configure the right Authentication Profile
Use https as the protocol and Port 5986
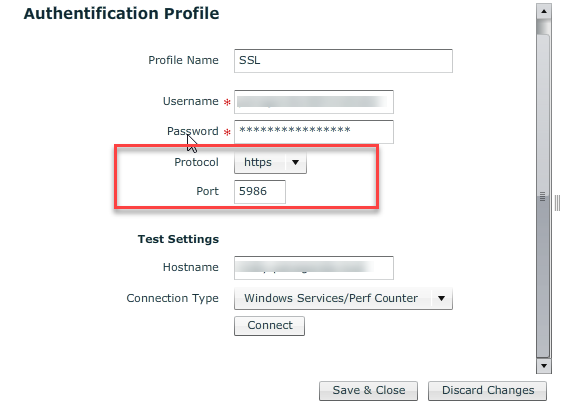
Test the Connection ....If everything is correct, you should get a "Success Message" back
Assign this Authentication Profile now to an Windows Host within GreenLight