Working from home, in a home office, wasn’t an entirely new thing in 2019. For instance, I do most of my business work from a remote home office location for more than a decade now. But the COVID-19 pandemic and resulting lockdowns in many countries forced a lot of companies to offer full-time work from home for the first time, often provided with only very basic knowledge of remote work security. Many organizations and employees were forced to move into the unfamiliar territory of work from home with almost no time for preparation. Neither for the organization nor the employee.
When moving your workplace from your company’s office to your home office, in most cases you leave the secured territory of your IT department. Working from home requires you to improve your cyber security to protect your personal and your corporate information. This article offers some easy-to-follow tips on how to improve your remote work security measures. It is a follow-up to our previous article Security Tips: A Personal Security Checklist and adds some info focused on working from home.
Cyber Security Statistics to Consider When Working From Home
- Cybercrime costs the global economy about 1 trillion — 50% more than that predicted in 2018. Also, it is more than 1% of the global GDP.
- The average cost of a data breach in 2020 was a whopping $3.86 million. In 2021 it was $4.24 million.
- A data breach compromising 1-10 million records costs $50 million on average, whereas one compromising 50 million records can cost as much as $392 million.
- A cyber-attack occurs roughly every 39 seconds.
- 445 million cyber-attacks were reported during the first three months of the pandemic — a 20% increase as compared to the previous quarter.
- By March 2020, there was over 650% increase in COVID-19-themed spear-phishing emails.
- In a recent survey, 45.5% of survey respondents claimed that their organization faced between one and five successful attacks during the past year.
- 69% are using personal laptops or printers for work activities.
- 70% of office workers admit to using their work devices for personal tasks.
- Almost one-third (30%) of remote workers have let someone else use their work device.
Physically Secure Your Workplace

When establishing your home office, we highly recommend, that you set up a couple of remote work security policies for yourself and all members of your household. First, use locks where ever and whenever possible. From a security perspective, having a dedicated area for productivity is almost a must. If you can lock your home office when away, then do it. If you cannot lock your office, use a lockable drawer for your devices, when not using them. And build the habit of locking your device’s operating system, whenever you are away from your desk. It also helps to enable automatic locking. Make sure to set an amount of time that while convenient is not unreasonably long. We recommend 30 seconds for mobile devices and five minutes for laptops.
You should also separate your work and personal devices as much as possible. If you use private devices, make sure to comply with your organization’s information security policies. It is a good idea to inform your IT department of the private devices you use. Some companies might have “Bring-Your-Own-Devices” (BYOD) policies that you might have to follow. And do not share your devices with other members of your home. If you have kids, you should not allow them to use your work PC or laptop unattended.
Network and Data Security
Your router is your doorway to your home network and the internet. And also, to your organization. Most routers today offer a firewall, wireless networking, and a broad list of security features. Some more expansive devices will include extra security options like a stateful packet inspection firewall, Denial-of-Service (DoS) protection, content filtering, and others. Some very important steps should be taken as soon as you take a new device out of the box.
Set Up Your Router
- Change your router’s default password. Many routers require you to change your password when first connecting to their web interface nowadays. Use a strong password to secure admin access to the configuration interface. If you have not done this, do it now.
- Set up a secure Wi-Fi network. You can use whatever SSID you want, but make sure to use WPA2 or WPA3 for communication encryption and set a strong password to protect your wireless network.
- Check for updated firmware regularly. Your router is your first wall of defense against cyber security attacks, so checking with the manufacturer once a month would be a good practice. If your router supports automatic updates, enable it.
Secure Data Storage
You will be accessing company resources from your home office. So, one of the primary considerations for data and remote work security is the location of where your data is stored. Especially as it is expected that your company has access to their data all the time. Many companies rely on secure cloud storage solutions like Dropbox, OneDrive, or iCloud. You have to comply with your organization’s policies on how and where to store data and should prevent storing work-related data on any of your private devices.
Virtual Private Networks (VPN)
Many companies use business VPNs to enable remote workers to access their internal company network. This is a particularly well-protected service against the interception of data – which is critical when working from home. In many cases, VPN client software is available for all kinds of devices, such as mobile phones and tablets, and operating systems like Windows, macOS, Linux, Android, or iOS. Your IT department will provide you with the necessary steps to add this very important measure to tighten your work-from-home cyber security.
Encrypt Your Devices for Enhanced Security
One thing you can do to enhance your cyber security while working from home is to encrypt the data on your devices. All this means is that this information will be inaccessible to everyone except those who have the key, which would presumably be limited to yourself and a few others. Here is a list of device encryption options for the most common operating systems:
Keep Your Operating System and Software Up-To-Date
To minimize the risk of zero-day exploits, ensure all devices apply security patches as soon as possible, ideally via automatic updates. Most modern devices will automatically apply updates by default, but you may need to allow your device to restart to complete the patching process.
The same reasons to keep your operating systems up to date apply to all installed software on your devices. You should pay special attention to the web browser you use and install each and every available security update. While most modern software today will check for, and apply security patches automatically, for some software it will be necessary to check for the latest versions manually.
Where possible you should consider using a secure SaaS application over installable software. It cannot become out of date and the management of security is in the hands of the provider rather than you.
Use Anti-virus or Anti-malware Software to Strengthen Cyber Security
Anti-Virus or Anti-Malware software can help protect your computer from viruses, spyware, ransomware, rootkits, trojans, worms, and other types of malware. Anti-Virus software is a very useful line of defense against the many threats that are out there and is a “must-have” for anyone working from home and worried about remote work security.
These programs not only do help you remove malicious software but also in case it finds its way onto your computer. They also perform real-time checks to alert you of potentially dangerous sites and links before you click them. They also put a step between downloading and installing programs from the internet. That will give you the chance to review that what you are doing is safe. In most cases, your company should provide you with some anti-virus software. If they do not, you should reach out to your IT department for support and recommendations.
Enable Find My Device…
Being able to find and ideally remote your device is a crucial part of ensuring information security when a device is lost or stolen. Securely wiping a device makes it much harder to access your data, no matter how much time or determination an attacker has. Here’s how to enable find my device for common operating systems:
- Windows: Enable in Settings > Update & Security & Find my device.
- macOS: Set up iCloud on your device by going to Settings > Your Name > iCloud > Find My Mac.
- Linux: Not built into the operating system and requires a third-party app
- Android: Set up a Google account on the device and it will be enabled by default.
- iOS: Setup iCloud on your device by going to Settings > Your Name > iCloud > Find My iPhone/iPad
…and Wipe Your Device. If Necessary, Remotely.
When lending, giving, selling, or just throwing out an old device, make sure to return it to factory settings. This will prevent your data from being accessed after you no longer have control over your device, temporarily or permanently. Before doing this, remember to back up or transfer any important information on the device. Here’s how to return your device to factory settings:
- Windows: Follow this guide from Microsoft and when asked, click remove everything.
- macOS: Follow Apple’s guide.
- Linux: Follow Arch’s guide then reinstall your distro.
- Android: Go to Settings > System > Reset options > Erase all data (factory reset).
- iOS: Follow Apple’s guide.
About Passwords
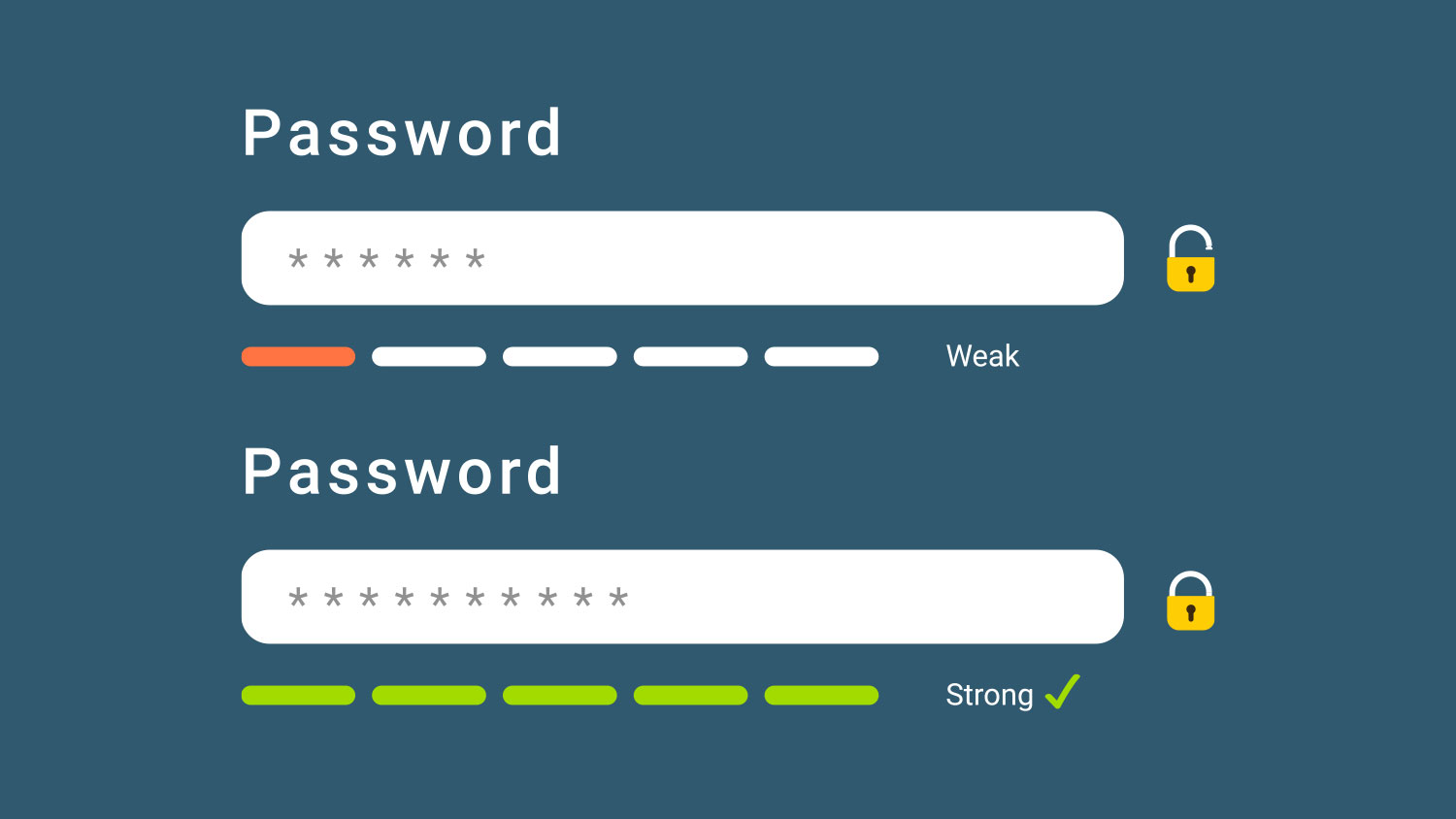
We already wrote a lot about passwords, authorization, and authentication in our previous security blog post, Security Tips: A Personal Security Checklist. The same recommendation on your personal cyber security checklist also applies to your remote work security measures. Use strong passwords. Do not share them. Change them regularly. If your company does not offer proper password management software, talk to your IT department or your Information Security staff and ask for it. It makes life so much easier for you AND your organization.
Stay Vigilant and Be Cyber Security Aware
While we all have new worries these days, our old worries – and cyberthreats – haven’t gone anywhere. One of the best ways to stay safe online simply requires remaining alert. Think of your home office as your “real” office. You should scrutinize all email messages and avoid clicking on any links or attachments, especially in unsolicited emails. They may be attempts to gain parts of your account credentials or to download malware onto the device. Be highly suspicious of urgent requests and verify them through an alternative communication channel before sending money or data. I doubt contact your IT department and ask for support.
It’s amazing what you can learn from down-to-earth podcasts or videos on security. There is a good list of free online courses about cyber security available at welivesecurity.com by Esset for you.

